Welcome to The Optery Dispatch — a newsletter delivering the latest insights on threat intelligence and proactive cybersecurity strategy. In Issue #12, published April 30, 2026, we cover:
- Identity threats surge as attackers prioritize identity compromise to access cloud systems, SaaS applications, and corporate AI tools
- The latest IC3 report shows that business-relevant cybercrime risk remained centered on impersonation, payment deception, and AI-assisted fraud
- A Black Basta-style campaign uses automated social engineering to target senior personnel and accelerate initial access
Red Canary: Identity Attacks and Direct Social Engineering Defined the 2025 Threat Landscape
Identity threats surge as attackers lean harder on browsers, tokens, and direct social engineering
Red Canary’s 2026 Threat Detection Report describes a threat landscape shaped by identity compromise, browser-based attack paths, direct social engineering, and growing attacker use of AI. Cloud accounts remained the top ATT&CK technique in its dataset, identity threats increased 850% year over year, and identity-based threats accounted for 53% of overall detection volume in 2025, up from 20% in 2024.
Red Canary says this rise reflects several factors, including broader adoption of identity products, improved detection coverage for risky logins, and better automation via agentic AI, but also notes that identities have become the most critical security boundary at most organizations, and adversaries are increasingly targeting them to access cloud systems, SaaS applications, and corporate AI tools.
On attack vectors, the report highlights a mix of phishing, credential abuse, token theft, browser-mediated techniques, and social engineering-driven payload delivery. It points to device code phishing, consent phishing, adversary-in-the-middle phishing, password spraying, credential stuffing, token theft, and MFA fatigue as recurring ways attackers gain or extend access. It also stresses that browsers have become a critical focal point because authentication increasingly happens there and because browsers store sensitive material such as cookie-based tokens.
The report says adversaries are using AI as a force multiplier rather than inventing wholly new attack techniques. Red Canary writes that AI is lowering the barrier to develop and conduct attacks, with adversaries using it to support reconnaissance, credential theft, data exfiltration, fraud, spear phishing, and the mimicry of individuals on phone or video calls. At the same time, it argues that defending against AI-enabled threats still comes back to familiar fundamentals such as least privilege, comprehensive monitoring, and defense in depth.
Red Canary’s ransomware analysis says 2025 saw wider use of aggressive social engineering by ransomware affiliates. The report specifically calls out help-desk targeting through voice phishing, email bombing followed by phone or Microsoft Teams contact, and the use of remote monitoring and management tools such as Quick Assist after the victim is manipulated into granting access. It also says adversaries are increasingly engaging employees more directly, including phishing the help desk, impersonating SaaS administrators, and, in one notable case, offering an employee a share of ransom proceeds in exchange for insider access.
That same pattern appears in Red Canary’s sections on infostealers and RMM abuse. The report notes that stealers were commonly delivered through phishing campaigns, compromised websites, cracked software, and malvertising, but that one of the most popular delivery methods in 2025 was “paste and run,” also known as ClickFix or fakeCAPTCHA. Red Canary says the vast majority of attempted LummaC2 deliveries it observed used malicious copy-and-paste techniques. Separately, its RMM section says these tools became the payload of choice for financially motivated attackers and ransomware affiliates, including in web-based phishing campaigns using lures such as fake browser updates, meeting invitations, party invitations, and fake government forms.
Red Canary also highlights malicious browser extensions as a growing enterprise risk. The report describes dangerous code spreading through trusted browser marketplaces and malicious updates to existing extensions, including supply-chain compromises of reputable extensions. In at least one case, Cyberhaven, the compromise began with social engineering against developers before a malicious update was pushed through the Chrome Web Store.
On mitigations, the report emphasizes familiar but important fundamentals: strengthen identity security controls, enforce least privilege, improve visibility across endpoints, cloud environments, SaaS apps, and browsers, monitor for risky logins and token abuse, educate employees on tactics such as email bombing and paste-and-run lures, patch internet-facing vulnerabilities, and maintain tight control over RMM usage by monitoring or blocking unauthorized tools. Red Canary’s broader message is that defenders still have the best chance of stopping these intrusions early, before exfiltration, encryption, or broader compromise occurs.
For organizations, the report reinforces a now-familiar pattern: attackers are targeting identities and the people behind them rather than relying only on software exploits. That makes it even more important to reduce the information adversaries can use to profile, target, impersonate, and manipulate employees in the first place. Removing exposed personal data from data broker and people-search sites is a strong proactive defense against today’s identity-focused attacks.
The FBI’s 2025 IC3 Report Shows Social Engineering Still Driving Major Enterprise Losses
The FBI’s latest cybercrime data shows impersonation, payment deception, and AI-assisted scams continuing to pose serious risk for organizations
The FBI’s 2025 IC3 report shows that business-relevant cybercrime losses remained heavily concentrated in fraud and impersonation-based schemes. Across all IC3 reporting, phishing/spoofing was the highest-volume crime type at 191,561 complaints, while business email compromise caused about $3.05 billion in losses. Tech/customer support fraud and government impersonation were also major categories, with 47,794 and 32,424 complaints respectively, together driving about $2.93 billion in losses.
The report also shows that these threats are evolving through AI-assisted deception. IC3 recorded 22,364 complaints containing AI-related information and about $893.3 million in losses in 2025. The FBI specifically notes AI can be used in BEC to generate official-sounding emails and cloned voices that pressure employees to make wire payments, and businesses alone reported more than $30 million in losses tied to AI-involved BEC. IC3 also recorded approximately 4,700 account takeover complaints with about $359.7 million in losses, while the report describes employment scam cases in which voice spoofing, or voice deepfakes, were used during online interviews in attempts to gain access to private company networks.
Taken together, the IC3 data shows that impersonation, payment deception, and account compromise remained major business-relevant risks in 2025, with AI making several of these tactics more scalable and convincing. For organizations, that reinforces the need to reduce the information attackers can use to profile, impersonate, and target employees in the first place.
Read the full report:
FBI: Americans lost a record $21 billion to cybercrime last year
Black Basta Returns? Senior Personnel Targeted in Accelerated Version of the Group’s Playbook
Automated social engineering campaign enables rapid initial access
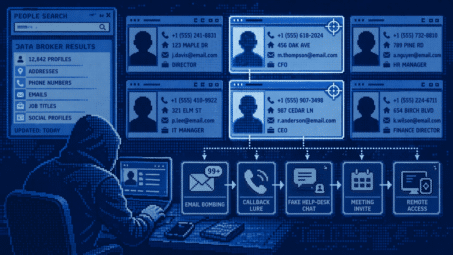
In a new report, ReliaQuest says a likely former Black Basta affiliate cluster is evolving the group’s social engineering playbook into a faster, more targeted intrusion method aimed at senior leadership. The campaign combines high-volume email bombing with Microsoft Teams-based help-desk impersonation to push targets into remote access sessions within minutes. From March 1 to April 1, 2026, 77% of observed incidents targeted senior-level employees, up from 59% in January and February, while 56% of all Teams-phishing activity observed since Black Basta’s decline in early 2025 occurred in the first four months of 2026 alone.
The report notes: “This campaign closely matches historical Black Basta activity in its manufacturing sector targeting, use of specific but alternating RMM tools, and reliance on a well-established social engineering workflow. At the same time, some downstream elements do not point cleanly to Black Basta alone: Extortion activity has aligned at times with “Chaos” ransomware, while some tooling and naming conventions align with “FIN7.” These overlaps suggest not a neat attribution, but a fluid ecosystem in which operators and playbooks are reused across groups…Our assessment is that it is highly likely former Black Basta affiliates are involved, either regrouping or collaborating with others.”
ReliaQuest says the campaign shows signs of growing automation, or at minimum a highly repeatable workflow. In some cases, attacker chats to different users were launched seconds apart, and the intrusion chain moved from inbox flooding to live remote access in as little as 12 minutes. The report also says the actors appear to be refining their open-web reconnaissance automation to improve target selection, especially around senior personnel.
We also know from the formerly leaked Black Basta chats that Black Basta has a history of using data brokers during reconnaissance for target selection and social engineering, a practice they share with other threat actors. If these affiliates are following the same playbook, we can reasonably expect that same pattern now.
ReliaQuest’s recommended defenses focus on breaking the attack chain before remote access is established: require strict out-of-band verification for any help-desk request involving remote access, enforce tighter controls around RMM tools through allow-listing and user restrictions, and run targeted simulation-based training for executives and managers.
This campaign is another reminder that social engineering defense has to start before the first message or phone call arrives. These Black Basta-style intrusion chains are built to move fast before defenders can take action. Removing exposed executive and employee data across data broker sites and other online sources disrupts attacker reconnaissance and helps prevent targeting.
Learn more:
Are Former Black Basta Affiliates Automating Executive Targeting?
Black Basta-linked attacks target executives via Teams phishing | news | SC Media
Thanks for reading! Want us to write about something specific? Submit a topic or idea.
If you’re looking to reduce your organization’s exposed PII and prevent phishing, voice and messaging scams, credential theft, and other PII-based threats, Optery can help. Get started here: Optery for business
Subscribe to receive future editions of The Optery Dispatch